Despite all the steps you may take to protect yourself, you will someday have to recover from an attack. In security, we say it’s not IF but WHEN. Every step we take to protect ourselves must have consideration for the recovery.
In this post I’m sharing what steps you can take after an attack. These steps will speed your recovery. If you planned in advance, you’ll be better prepared and reduce the impact of a successful attack. I’ve included Preparation Steps for each area of recovery.
Start Here: Basic Attack Recovery Steps
The following are steps you should take any time your account has been breached. There’s no need to wait on these steps at all, and they should be performed immediately. There are other steps below for different kinds of attacks but this is always the starting point.
Document Your Process
Get that notepad out (yes the one you write on with a pen or pencil). You will want to document the steps you’re taking and the results. You’ll want to document the names of people you spoke to during the attack and during the recovery. These may be important as you proceed through the recovery and to resolve issues afterward.
You may also wish to start a list of tasks to check off. You may find more issues to resolve as you proceed through recovery.
Check your Email
First step of your attack recovery is that you’ll want to check your email. There are many reasons to do this:
- Ensure you still have access – you’ll be getting password reset emails and other information. We want to make sure a hacker hasn’t denied access to your email.
- Check for alerts – there may be clues into what the attacker has done, and what you’ll need to undo it.
- If your email password is the same as any other passwords you have, it is a good idea to change it right away. Also if your email service offers 2 factor or multi-factor authentication, it’s a good idea to set that up now.
Preparation Steps:
- For each account, know which email is associated. Some of us have many different email addresses. Knowing which one is for which account will be helpful. Store this information offline.
Change the Password
Log into the attacked account and change the password. If the account offers 2 factor or multi-factor authentication, it’s a good idea to set that up now.
Was your computer compromised? Make sure you change that password.
If you can’t log in due to the attacker changing the password, you can change the password if the recovery email is unchanged. From the login prompt, choose the “lost password” or “I forgot” option. That should send a password recovery email to your email (which you validated in the previous step).
Preparation Steps:
- Use a password manager to store all your account information to make recovery faster.
- Use 2 factor or multi-factor authentication to protect your accounts in the event of a password breach.
- Use a complex password for your computer. Do not rely on the fact it is secure in your home. Clicking a link online can actually expose your computer and the hacker can control it as if they were in your home.
Financial Recovery
You may have to follow these steps in a few different scenarios. Speed is of the essence in financial attacks since the funds from some accounts may take a long time to recover.
- This was a phone scam and you gave your credit card number.
- This was a phishing scam and you logged into a fake bank login page, revealing your login and password.
- This was a compromised merchant account like Amazon, Doordash, or another account that stores payment information.
The recovery steps here are to follow the basic steps above, and then to contact your financial providers to take steps to protect your accounts.
If you don’t have fraudulent charges yet, it is best not to wait to report.
You can check the back of your credit cards for the number to call for a stolen number. You’ll be asked about recent transactions which might not be reported yet.
Cash Accounts
You’ll want to take special care with these accounts. They include checking, savings, retirement, money market and others. Any account that you can transfer funds in and out of may also be part of the compromise.
- Call the account provider – let them know what happened, so they can take steps to lock down your assets.
- Review your accounts – after you lock the accounts down review them (online if possible) and note any conspicuous charges for further reporting.
Preparation Steps:
- Keep a list of the name of a credit card (not the number) associated with each of your online accounts (offline of course). This way you’ll know right away which cards to report as stolen. Include the phone number to report a stolen card.
- This is also makes it easier to set your automatic payments back up. Some billers will charge late fees if your card has been canceled.
- Keep a list of phone numbers for your bank, investments and other cash accounts handy for quick access.
- Set up notifications on your accounts to email you when purchases are made on your financial accounts. This may tip you off in advance of a successful attack.
- Consider using a special credit card for online purchases only.
Identity Recovery
The nature of an identity theft makes it quite tedious and difficult to determine what exactly you need to do in order to recover from it. There is an online resource with the US government which shows an excellent set of steps to follow: https://www.identitytheft.gov/#/Steps You may also report the identity theft on the same site to enable government resources to help in your recovery if you choose.
Here are some key areas I’ve helped others with and what the steps are:
Credit Monitoring
You may have heard you can get a free credit report. If you don’t have one, it’s always good to get a copy each year for review. The website is https://www.annualcreditreport.com
- Check that the accounts are true and correct. Report anything incorrect.
- Check the addresses of record for your identity. Hackers will often set an address up
Preparation Steps:
- Get a copy of your credit report so you can compare it against another copy after a suspected identity theft. It will be easier to identify improper entries. Renew it annually: https://www.annualcreditreport.com
- Get free credit monitoring which will notify you of any changes to your credit records. This could alert you quickly to identity theft. Quick recovery is key since recovery can take a long time. Beware the services you choose.
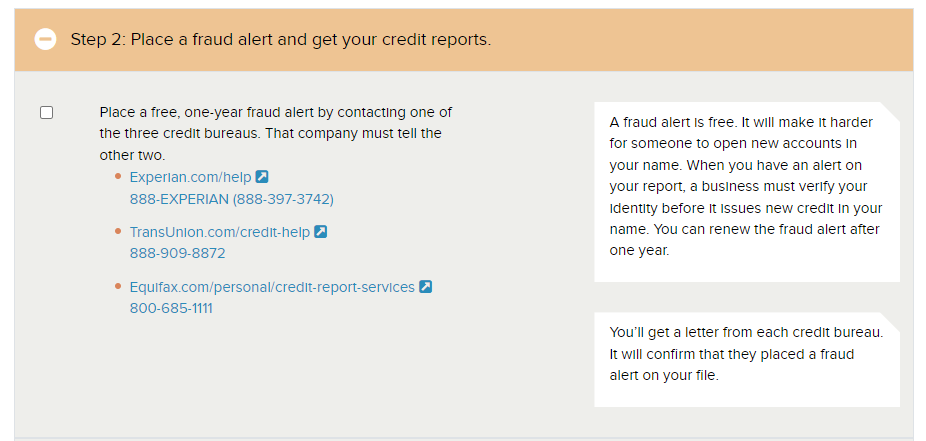
- Consider setting a fraud alert through one of the three credit bureaus. It’s free and is set for 1 year. You can renew it after it expires. You can do so as shown on this image from the identitytheft.gov site:
The government resource above (https://www.identitytheft.gov/#/Steps ) will be key in recovery. One of the few ways your social security number is used is to file a tax return in your name. The hacker needs your number and it’s even better for them if they can change your address. Doing so from the credit bureaus helps validate the address. They file the return and get a refund in your name.
Data Recovery
The data I’m referring to are the files and documents you have on your computer and/or in the cloud.
There are many ways your data can fall under attack in these places. They can involve hacking into your computer, using a compromised password to a cloud resource, and others.
Generally, the attacker is using your data as ransom. They’ll make the data inaccessible in some way (deletion, encryption, or another method), and demand payment.
I don’t advocate paying ransoms because most don’t release your data.
The best recovery is to restore your data from a backup. However, I know many folks may not be backing up the data. This one is all in the…
Preparation Steps:
Cloud storage is great way to back up your data. The data exists both on your computer(s) and in the cloud. If the computer is compromised it’s possible to recover from the cloud. Some cloud storage is free for small data amounts.
If you don’t want to pay for a larger amount or don’t trust the cloud (it’s pretty trustworthy), then purchase an external hard drive that is sufficiently sized for the data you wish to protect. A good starting point is finding a drive which is as large as the storage drive within your computer.
How to best prepare?
- Get a cloud storage account for the most important data you need to protect. It should:
- Offer recovery in the event its deleted by a hacker.
- Uses strong encryption between your computer and the cloud.
- Encrypts your data in the cloud.
- Get an external hard drive or backup device to store important data. It should:
- Be tested monthly so you know your data is recoverable.
- Be large enough to store all your data.
- Use backup software which has protection from encryption by ransomware (you may have to ask the developer for details).
Wrapping Up
In this article I shared ways you can recover from a number of attacks. The key point is to reach out for help. Our interconnected world requires that we get assistance from others in the event of these kinds of attacks.
In addition, I have a number of tips about how to prepare for an attack recovery and better protect you.
If you have questions please ask or watch for an upcoming webinar or livestream!
